Excel Template
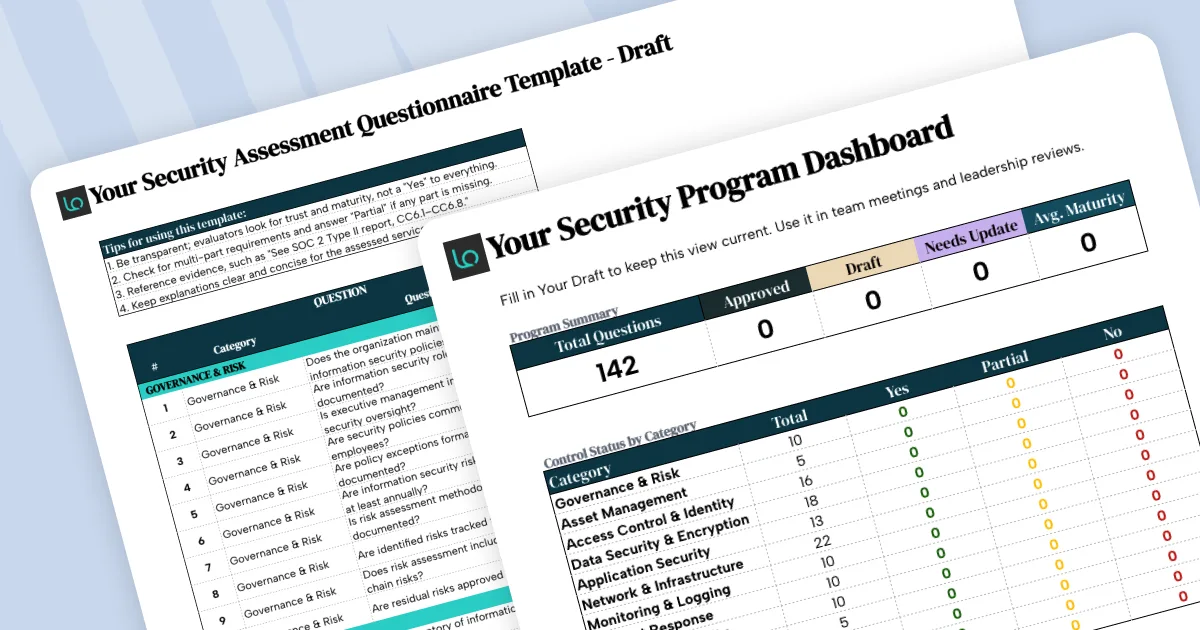
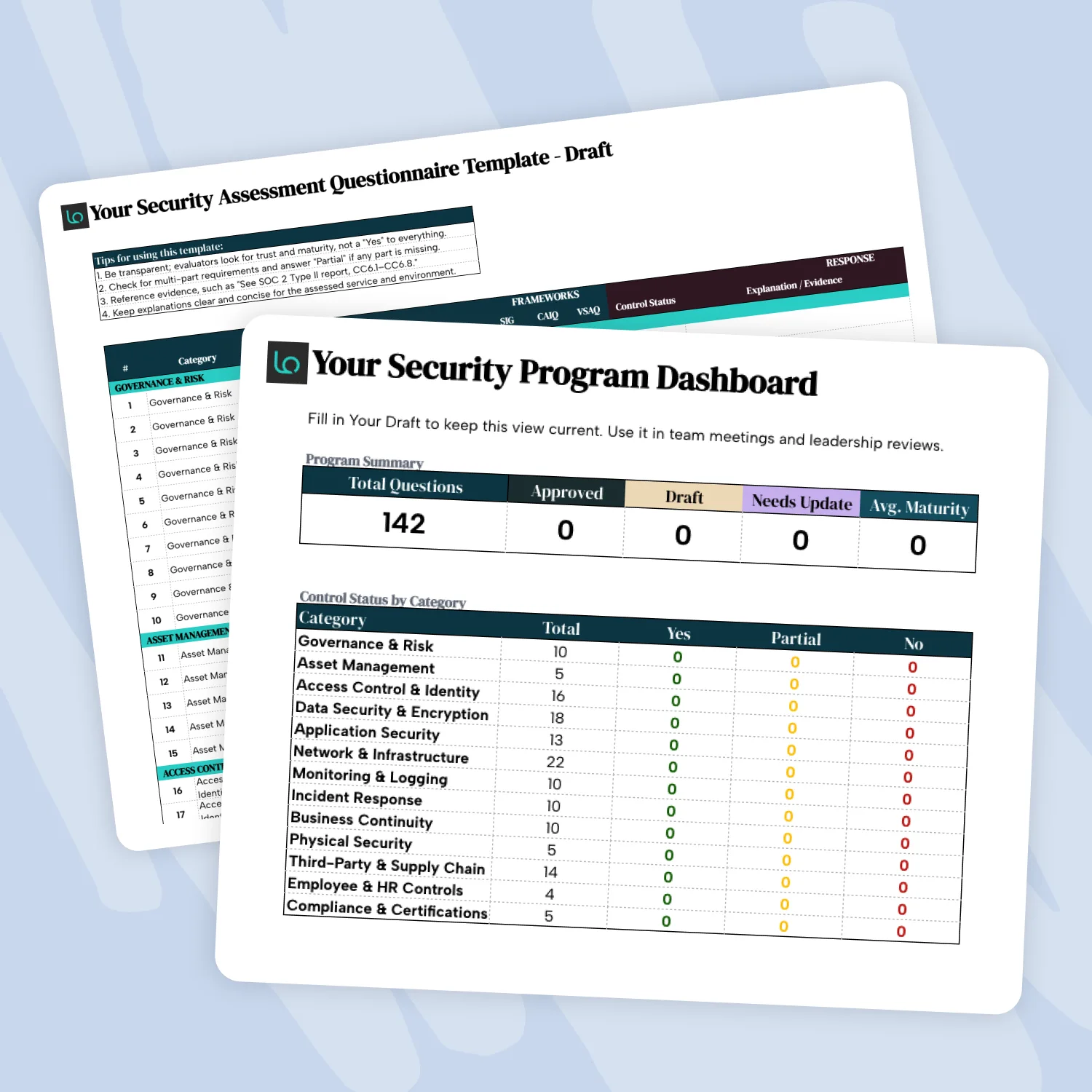
142 Security Assessment Questions
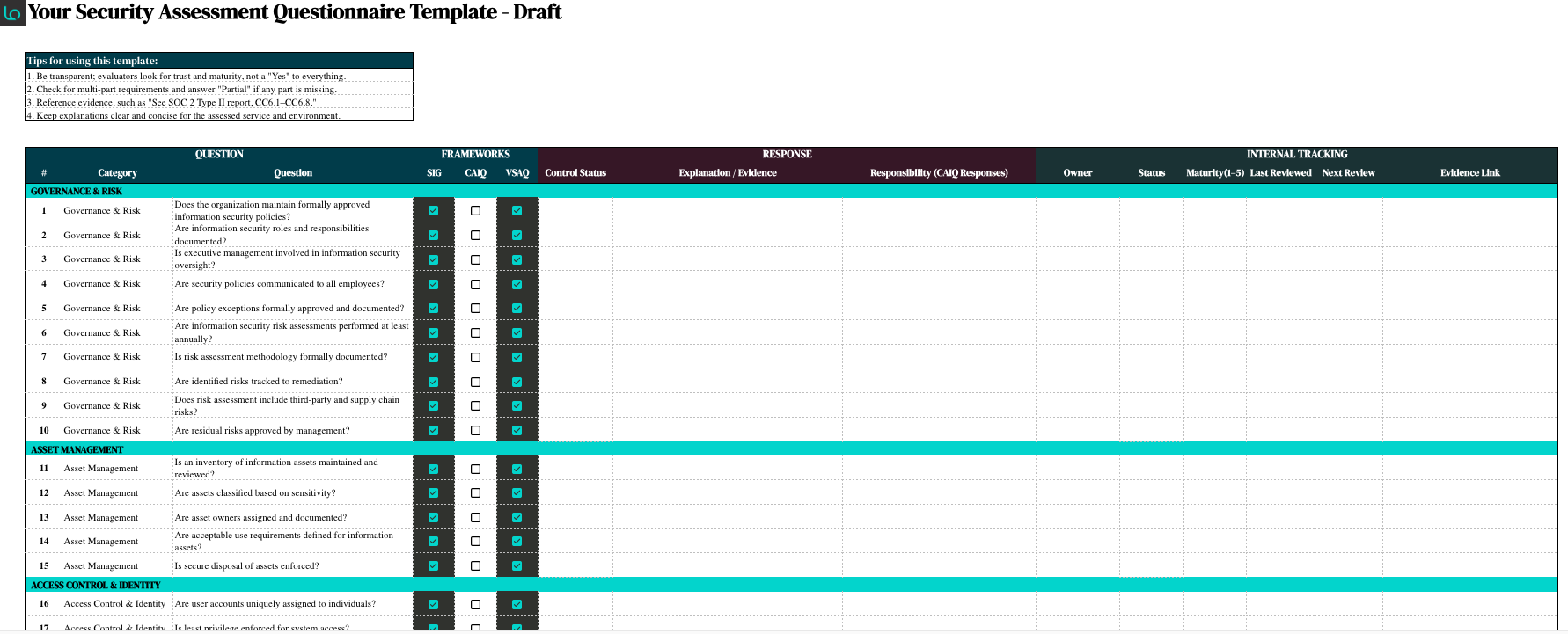
Answer once, reuse for every security questionnaire. Build a definitive response library mapped to SIG, CAIQ, and VSAQ frameworks.
Eliminate Repetitive Work With This Security Questionnaire Template
Most security questionnaires cover the same ground. This template allows you to draft answers to frequently asked questions—so every review goes faster, and every response stays consistent.
Fill it in once. Update it regularly. Pull from it every time.
Defensible Answers
Document your control status and link to supporting evidence—so every answer is defensible, not just claimed.
Always Audit-Ready
Assign owners and set review dates so your security documentation doesn’t go stale between assessments.
Zero Surprises
Identify where your security program is strong, where it’s developing, and where gaps need to be addressed.
How Do You Use This Template?
This template walks you through how to build a dual-purpose security hub—a response library where you can retrieve and reuse answers for incoming assessments, and a living record of where your security program stands today.
Simply follow these instructions:
1. Map an Incoming Questionnaire to the Template
When you receive a new security questionnaire (SQ), identify which questions in the template align with what’s being asked.
Most enterprise SQs draw from one or more frameworks, so many questions will already have a home in the template. For questions that fall outside the mapped frameworks, add them to the relevant category section.
2. Set Your Control Status for Each Question
For every question, record your control status: Yes, no, or partial.
Use partial when a control exists but isn’t fully implemented, or when a multi-part question is only partially addressed. Evaluators expect nuance, and a well-explained partial is more credible than an unsupported yes.
3. Document Your Response and Link to Evidence
Use the explanation / evidence column to summarize your response and reference supporting documentation such as SOC 2 report sections, ISO 27001 certification scope, internal policy names, or audit findings.
Specific references, such as “See SOC 2 Type II report, CC6.1–CC6.8,” carry more weight with evaluators than general claims.
4. Assign Owners and Review Dates
Assign an owner to each control and set a last reviewed and next review date.
Security policies and technical controls evolve rapidly. If answers no longer reflect current practice, they’ll become a liability when a questionnaire arrives.
5. Rate Your Maturity Level
Use the maturity column (1–5) to score the strength of each control.
This is for internal use: It helps you prioritize improvement efforts, identify where your program has gaps, and track progress over time. It also prepares your team to answer follow-up questions from buyers about the depth of specific controls.
6. Reuse for Every Security Questionnaire
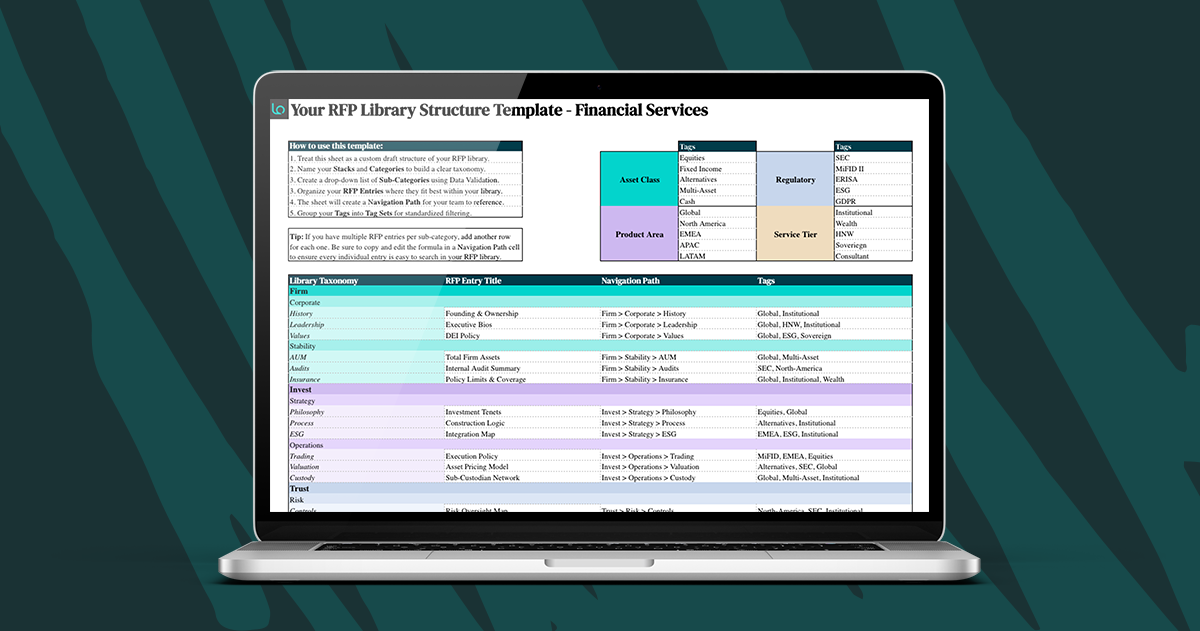
Once the template is populated, it becomes your answer library.
When the next questionnaire arrives, match questions to existing responses, update anything that has changed, and export or copy relevant answers directly. The goal is to spend less time starting from scratch and more time refining responses that already exist.
What’s Inside This Security Assessment Questionnaire Template?
As you may have guessed, this template gives your team a single place to document controls, manage responses, and maintain an up-to-date record of your security program. This template includes the following:
✓ A pre-built library of 142 questions organized across eleven categories and mapped to SIG, CAIQ, and VSAQ frameworks to help you instantly identify which controls apply to any incoming assessment.
✓ Control status and evidence linking to document your security posture, summarize your responses, and link directly to supporting proof.
✓ Ownership and review cadence to designate owners and set review dates, ensuring your documentation remains current and accountability is clear.
✓ A security dashboard that tracks your average maturity and control status across categories, providing a real-time view of your program’s strength.
Who Is This Risk Assessment Template For?
This template is designed for teams that regularly respond to vendor security reviews and need a faster, more consistent way to manage them.
- InfoSec teams can use it to document controls, maintain evidence links, and keep the organization’s security posture up to date between reviews.
- Proposal and sales teams can pull from it when security questionnaires arrive as part of an RFP response process, without having to chase down answers from technical teams.
- IT and compliance teams can use the maturity scoring and review cadence columns to track program development and prepare for audits.
For a deeper look at how to handle vendor security reviews end-to-end, read our guide to how teams can avoid security questionnaire bottlenecks.
“Loopio has greatly enhanced our ability to respond to Security Questionnaires and has provided great value in terms of efficiency and decreasing the effort of having to create answers over and over again.”

Download Your Copy Now
Preparing form…
FAQs About Security Assessment Questionnaires
A security assessment questionnaire is a structured set of questions that buyers, procurement teams, and enterprise customers use to evaluate a vendor’s security posture before entering or renewing a contract.
Questions cover areas like access control, data encryption, incident response, and third-party risk management. The goal is to give the buyer enough information to assess whether working with a vendor introduces unacceptable security or compliance risk
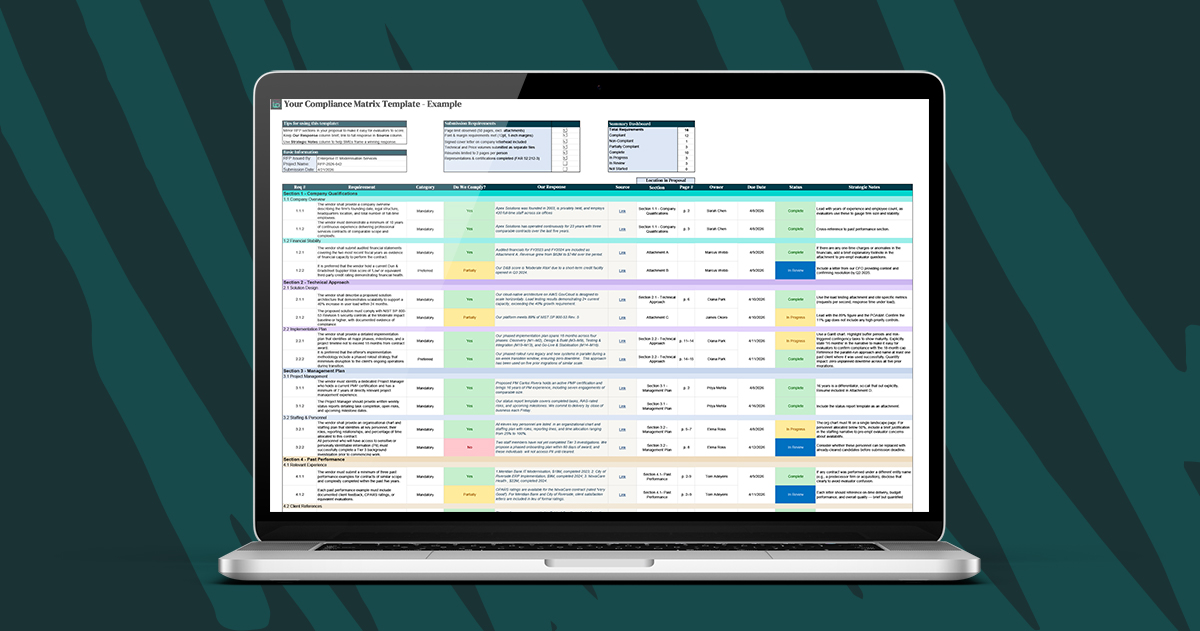
A security questionnaire is completed by a vendor to demonstrate the strength of their security program to a buyer.
A compliance matrix is used internally by a proposal team to track whether their RFP response addresses every requirement set by the buyer. They serve opposite directions of the same procurement process; one proves your security posture, the other ensures your proposal is complete.
If you need to build the latter, we have a compliance matrix template, too.
SIG, CAIQ, and VSAQ are three widely used security questionnaire frameworks, each developed by a different organization for a different primary audience.
The SIG, or Standardized Information Gathering questionnaire, is maintained by Shared Assessments and is commonly used by financial services, healthcare, and enterprise procurement teams to assess third-party risk in a detailed, structured way.
The CAIQ, or Consensus Assessments Initiative Questionnaire, is published by the Cloud Security Alliance and is designed specifically for cloud service providers. It maps directly to the CSA Cloud Controls Matrix and is frequently used by buyers evaluating SaaS and infrastructure vendors.
The VSAQ, or Vendor Security Assessment Questionnaire, was developed by Google and is used primarily in technology vendor assessments. It is open source and focuses on practical security controls across web applications and infrastructure environments.
Many enterprise buyers combine elements from more than one framework, which is why this template maps each question to all three.
In practice, it should be updated any time a meaningful change occurs.
For example, when a new certification is obtained, a control is implemented or deprecated, a security incident occurs, or your infrastructure changes significantly.
Teams that treat the template as a living document rather than a one-time project find that responding to new questionnaires takes a fraction of the time because answers already reflect current practice.
It depends on the framework, the depth of questions, and how well your security documentation is organized.
A first-time completion of a comprehensive security questionnaire like the SIG Core can take several weeks when coordinating across security, IT, legal, and compliance teams.
With a populated template and a maintained evidence library, the same questionnaire can often be turned around in days. The goal of this template is to front-load that effort so subsequent assessments get progressively faster.
That said, security questionnaire software is the fastest option available. It can help you complete a security assessment questionnaire in hours, not weeks.